Recharge Trust Center
We’re proud to share our privacy, security, and compliance initiatives with you here.
Privacy
Putting your privacy first
Our merchants and partners can trust that we value privacy and comply with standards like GDPR and CCPA. Learn more about how we handle personal information in our policies and agreements.
Security
Building security into everything we do
Security is central to our business. We use rigorous practices, processes, and tools to protect your data and continuously strengthen our platform.
-
Our services are maintained and hosted on Google Cloud Platform (GCP), which complies with an independently verified set of standards and frameworks (for example, PCI DSS, SOC 2&3, ISO 27000). About Google Cloud Security.
-
We maintain an active bug bounty program and contract with third-party organizations to conduct regular security tests to validate the effectiveness of our security controls. While our security team conducts frequent security reviews, we also encourage independent vulnerability reporting through our responsible disclosure page.
-
Our product development teams follow standardized processes with built-in security checks as well as complete security training programs to stay consistently vigilant for ways to maintain secure products and services.
The Recharge product security framework combines a holistic and practical approach that integrates security best practices throughout each phase of the software development process.
-
We have designed and continue to make significant investments in operations to achieve optimum security and ongoing compliance of our services. We combine automation and skilled reviewers to filter intelligence from many sources to determine the necessary course of action. Our operating procedures include:
- 24/7 incident handling with defined escalation paths
- Data encryption (including TLS and AES256) at rest and in transit
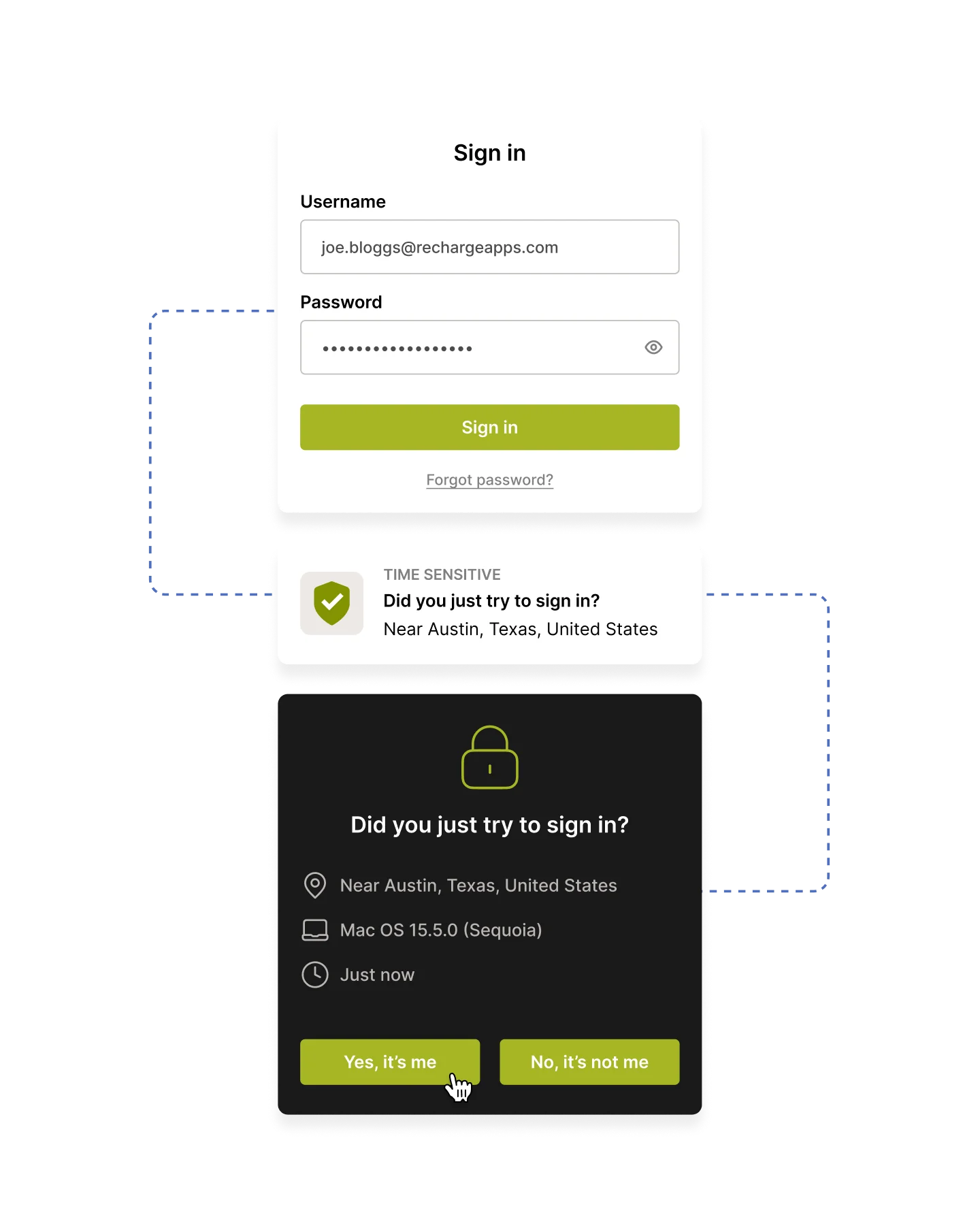
- Secure system access management with multi-factor authentication
- Logging, monitoring, and alerting
- Vulnerability and patch management
- Security testing to identify and remediate vulnerabilities
- Maintenance and backup procedures
Availability & uptime
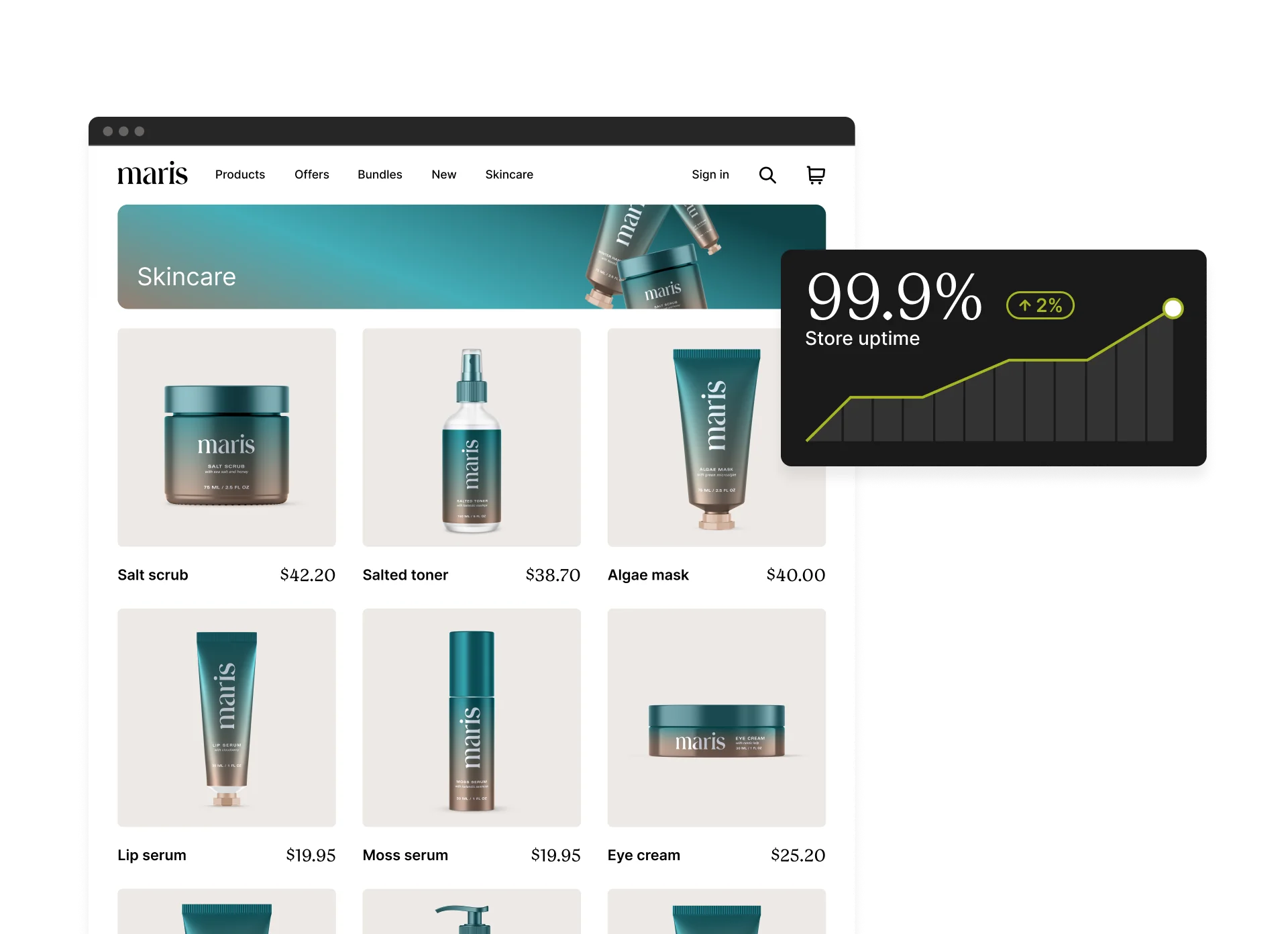
Keeping your business online
Recharge runs on Google Cloud Platform (GCP) with a focus on availability and resilience. Our recovery strategy leverages GCP’s global infrastructure to meet Recovery Time and Recovery Point Objectives (RTO and RPO).
We also provide a public status page with real-time and historical system performance, availability, and maintenance updates.
Compliance
Adhering to industry standards
Beyond our hosting platform’s compliance, Recharge meets key industry standards to protect your data. We are Payment Card Industry Data Security Standard (PCI DSS) certified and maintain a Service Organization Control (SOC2) Type II report verifying our controls.
We also take active steps to monitor that our platform is usable by all individuals and review compliance with relevant standards, including the Americans with Disabilities Act (ADA).


Get started
Start a free trial of the subscription platform trusted by over 100 million subscribers across the world.